- ISO 27001
- 13th Apr 2026
- 1 min read
ISO 27001 Annex A.8: Technological Controls Guide

- Written by
In Short...
TLDR: 4 Key Takeaways
- Annex A.8 differs by ISO 27001 edition—technological controls in 2022 vs asset management in 2013
- Most failures come from execution gaps, not control design—registers, SoA, and evidence drift over time
- “Implemented” must be backed by current, linked evidence or it won’t stand up in audit
- Strong programmes treat assets and controls as continuous governance, mapping once across ISO, DORA, and NIS2
Introduction
Most teams searching "ISO 27001 Annex 8" are looking for two different things — and the answer depends entirely on which edition of the standard they're working from.
In ISO/IEC 27001:2022, Annex A.8 is the Technological controls theme — 34 controls covering access, configuration, monitoring, backup, and your software development lifecycle. In ISO/IEC 27001:2013, "A.8" was Asset management: inventory, ownership, classification, and acceptable use.
The 2022 revision moved asset management controls into A.5 (Organisational controls) and reorganised 114 controls into 93. If your team is still working from 2013 playbooks, you are mapping to a structure that no longer exists. This guide covers both.
It also covers where most implementations fail. The IBM Cost of a Data Breach Report puts the global average breach cost at USD 4.88 million. That figure reflects what happens when controls, asset registers, and evidence diverge from operational reality. Technical controls are only as strong as the governance that keeps them current.
What Is ISO 27001 Annex A.8?
In ISO/IEC 27001:2022, Annex A.8 is the Technological controls theme — one of four themes in the 93-control Annex A set. It covers the technical safeguards that protect your information systems: identity and privilege management, endpoint security, configuration, backup, monitoring, data leakage prevention, and secure development. If a control relates to how your technology is configured, operated, or defended, it is almost certainly in A.8.
In ISO/IEC 27001:2013, A.8 was Asset management — the controls covering inventory of assets, acceptable use, ownership, return of assets, classification, and labelling. In the 2022 edition, these controls were moved to A.5 (Organisational controls), with media-handling elements distributed across the Technological controls theme.
Your Statement of Applicability must reflect whichever edition your certification is based on. If you are mid-transition from 2013 to 2022, the two sets of control numbers are not interchangeable.
Editor's note: Confirm the current transition deadline with your certification body. The IAF's communiqué MD 26:2023 governs the mandatory migration period from 2013 to 2022. Most CBs set October 2025 as the final transition date — verify this is still operative and has not been extended.
The 10 Annex A.8 Controls Most Teams Implement First
The Verizon Data Breach Investigations Report consistently shows that the human element is present in the majority of breaches — through compromised credentials, misconfigurations, and unpatched systems. The ten controls below address those failure points directly. They give you fast wins, clean evidence, and a defensible starting position for your SoA.
A.8.2 — Privileged access rights Focus: admin accounts, break-glass procedures, service principals. Baseline: PAM and MFA on all high-risk access, session logging, quarterly access reviews. Evidence: PAM configurations, admin access attestations, session logs. SoA line: Applicable due to admin access to critical systems; PAM and MFA enforced; reviewed quarterly.
A.8.7 — Protection against malware Focus: endpoint detection across all platforms including macOS and Linux. Baseline: real-time protection, sandboxing, gateway filtering, blocklists. Evidence: EDR deployment report, blocked-threat summaries, exception register. SoA line: Applicable due to endpoint and email exposure; EDR and gateway controls active; metrics reported monthly.
A.8.9 — Configuration management Focus: define and enforce secure baselines across production systems. Baseline: CIS-aligned images, infrastructure-as-code, drift detection. Evidence: baseline documentation, drift reports, IaC pull-request history. SoA line: Applicable across production systems; baselines enforced; exceptions documented.
A.8.11 — Data leakage prevention Focus: exfiltration via email, cloud storage, and SaaS applications. Baseline: DLP for mail and cloud storage, sensitive-pattern tuning, monitored exceptions. Evidence: policy configuration, incident trends, tuning changelog. SoA line: Applicable due to regulated data in scope; DLP active; triage process defined.
A.8.13 — Information backup Focus: ransomware resilience and recovery capability. Baseline: 3-2-1 backups, immutable storage, quarterly restore tests. Evidence: job logs, immutability settings, restore test records. SoA line: Applicable for production data; immutable backups and quarterly testing in place.
A.8.16 — Monitoring activities Focus: prove detection works, not just that monitoring exists. Baseline: centralised logging across auth, network edge, endpoints, and cloud; defined alert use-cases. Evidence: SIEM use-case library, alert runbooks, sample incident records. SoA line: Applicable due to external exposure; centralised logging with defined alerts and coverage KPIs.
A.8.28 — Secure coding Focus: shift defects left into the development pipeline. Baseline: SAST/DAST in CI/CD, secrets scanning, threat modelling for major changes. Evidence: pipeline reports, PR approvals, defect remediation SLAs. SoA line: Applicable for in-house development; pipelines enforce checks; remediation tracked.
A.8.29 — Security testing in development and acceptance Focus: pre-production assurance before systems go live. Baseline: risk-based penetration tests, abuse-case testing, rollback plans. Evidence: test plans, pen-test reports, retest confirmation for critical findings. SoA line: Applicable for internet-facing systems; testing required before go-live; retest required for critical findings.
A.8.1 — User endpoint devices Focus: remote and distributed workforce security. Baseline: MDM/EDR, disk encryption, screen-lock, USB policy; coverage includes contractors. Evidence: device inventory, MDM profiles, encryption attestations. SoA line: Applicable due to distributed workforce; endpoint controls enforced through MDM and EDR.
A.8.32 — Change management Focus: disciplined change reduces outages and unplanned risk. Baseline: risk-based approvals, backout plans, post-change monitoring. Evidence: CAB minutes, change tickets, post-change checks. SoA line: Applicable across production; changes tracked and approved; periodic audits performed.
2013 to 2022: Where Asset Management Controls Moved
If your team is working from older documentation or a 2013-era SoA, the control numbers will not match the 2022 standard. This is not a minor admin change. Justifications built around 2013 groupings may no longer be accurate, and auditors expect the 2022 structure.
|
2013 A.8 (Asset management) |
2022 location |
|
Inventory of assets |
A.5.9 — Inventory of information and other associated assets |
|
Acceptable use of assets |
A.5.10 — Acceptable use of information and other associated assets |
|
Return of assets |
A.5.11 — Return of assets |
|
Classification of information |
A.5.12 — Classification of information |
|
Labelling of information |
A.5.13 — Labelling of information |
|
Removable media, disposal, media transfer |
Distributed across Technological controls (backup, DLP, secure deletion) |
What auditors expect to see on asset management. A current asset register with named owners. Acceptable-use acknowledgements. Return-of-assets records. Classification policy applied to real data samples — not just described in a policy document. Disposal certificates. A reconciliation method that proves the register is current, not a snapshot from the last audit cycle.
How to Write SoA Entries for A.8 Controls
A Statement of Applicability entry for a technological control is a decision record, not a description. It must tell an auditor — in one pass — why the control applies, what is in place, and where the proof is. Controls that require an explanation longer than two lines are usually trying to compensate for gaps in implementation.
Example SoA entry: A.8.9 — Configuration management
|
Field |
Content |
|
Applicability |
Applicable |
|
Status |
Implemented |
|
Justification |
Production and cloud systems process regulated data; unauthorised change and misconfiguration are assessed as high-likelihood risk vectors |
|
Linked risks |
Unauthorised change; vulnerability exploitation; supply-chain misconfigurations |
|
Evidence |
Baseline documentation, drift reports, IaC pull-requests, quarterly attestation |
|
Owner |
Head of Platform Engineering |
|
Review cadence |
Quarterly |
Keep three variants in your SoA: Implemented (with current evidence), Partially Implemented (with a remediation plan and target date), and Not Applicable (with a justification and, where relevant, a compensating control). One clear line of reasoning per control produces a more defensible SoA than a lengthy narrative without evidence.
Asset Registers Decay: Treat Inventory as a Continuous Process
An asset register is only accurate at the moment it was last updated. For most organisations, that means it starts decaying the day after the audit. New SaaS subscriptions appear outside procurement. Cloud resources spin up without tagging. People join, move roles, and leave. Suppliers extend or change their scope. None of these events automatically update a spreadsheet.
CISA's Binding Operational Directive 23-01 requires US federal agencies to perform automated asset discovery at minimum every seven days. The rationale is simple: environments change continuously, so the inventory must too. Your SoA loses credibility the moment your asset register diverges from what is actually running.
Turn static inventory into continuous governance by:
- Connecting operational sources — IdP/SSO, cloud provider APIs, device management (MDM/EDR), ticketing, and procurement — so the register updates as the environment changes rather than waiting for manual input.
- Automating ownership with attestations and escalation workflows when roles change, so every asset has an accountable owner at all times.
- Tracking register currency with review dates, sampling, and trend metrics so you know where drift is accumulating before your auditor does.
- Reconciling continuously so deltas generate work immediately, not at the next recertification.
The register is not a document. It is a governance function. Treat it accordingly.
Cloud and SaaS Assets: Govern What Actually Runs Your Business
Most environments are hybrid and multi-SaaS. Shadow IT and ungoverned SaaS subscriptions are among the most common sources of unmanaged risk in mid-market and enterprise organisations. If a SaaS application processes your data, it is an asset — regardless of whether it went through a formal procurement process.
For each SaaS application in scope, your register should capture:
- Named owner and team
- Data types processed and sensitivity classification
- SSO coverage (and what is not covered)
- Export, retention, and deletion settings
- Vendor responsibility statement (what the supplier controls and what you still own)
- Interconnections: which internal systems feed data into this application
Shared responsibility does not transfer accountability. When a cloud provider experiences an incident, your obligation to your regulator and your auditor does not disappear. Document what the provider controls. Document what you control. Then show the evidence for the part that is yours: identity and access management, monitoring, configuration, and incident handling.
Keep evidence simple and current: admin access logs, SSO coverage percentage, DLP incidents by application, and restore or retention settings where relevant.
Regulatory Leverage: Aligning ISO 27001 A.8 with DORA and NIS2
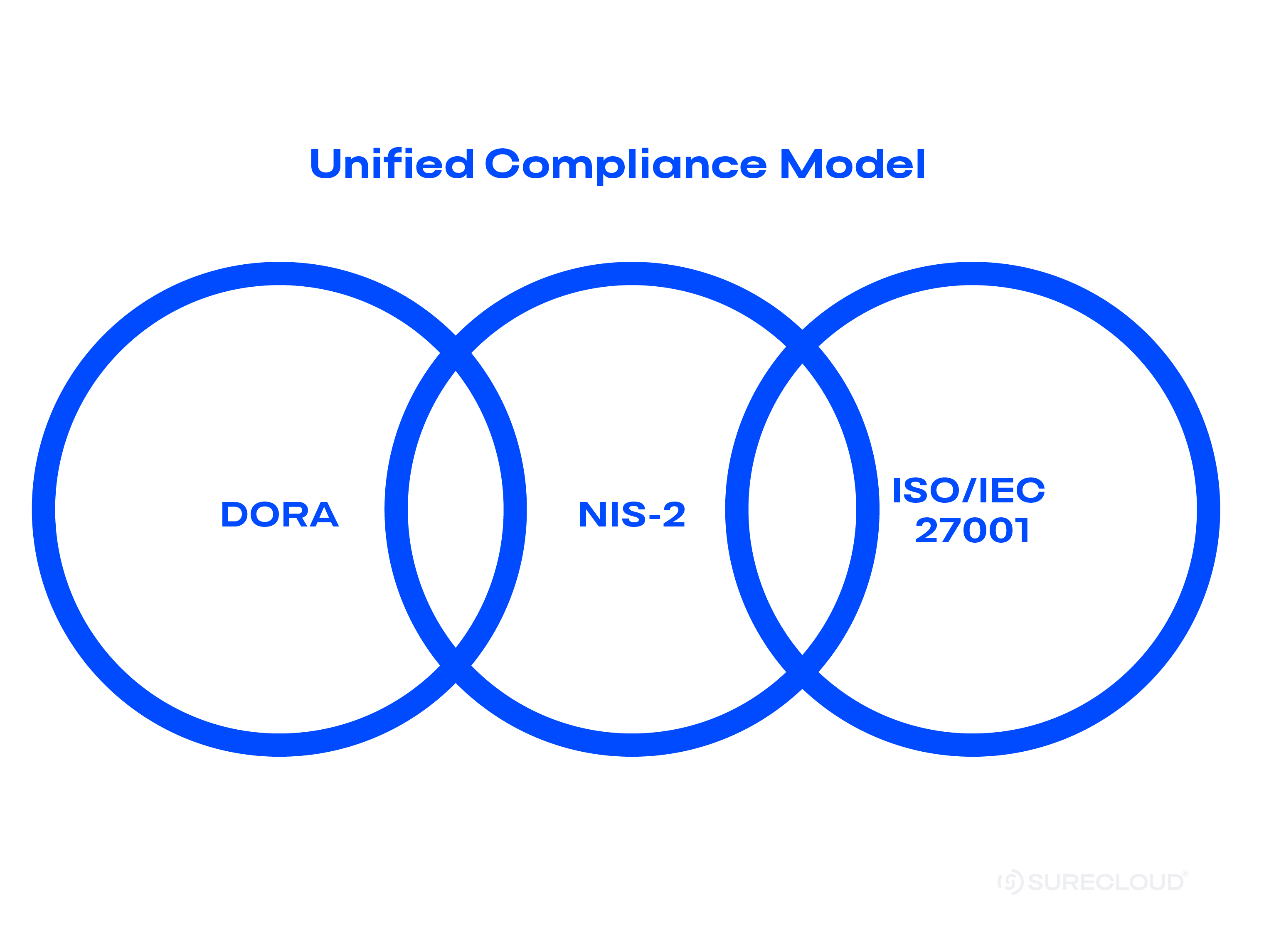
ISO 27001 Annex A.8 does not exist in isolation. DORA requires a policy for managing ICT assets as part of the ICT risk framework, with specific obligations around ICT third-party risk management. NIS2 requires risk-management measures that include asset identification and supply chain security. The underlying controls — inventory, ownership, configuration, monitoring, incident response — are the same across all three regimes.
The duplication trap is building separate evidence trails for each framework. The alternative is to build one register, tag each asset to the frameworks it touches, and produce ISO, DORA, and NIS2 views from the same live data. Evidence is attached once. It serves all three.
Why this matters now. DORA enforcement is active. NIS2's full compliance deadline is October 2026, with national transposition already underway across EU member states. Your ISO 27001 controls work is not separate from your regulatory programme — it is the foundation of it.
Editor's note: DORA Register of Information submission dates and NIS2 national transposition deadlines vary by jurisdiction and entity type. Verify current obligations against the EBA's DORA guidance and your relevant National Competent Authority before publication.
Where SureCloud Fits
The execution gap in A.8 compliance is not usually a knowledge problem. Teams know what the controls require. The problem is keeping the register, the evidence, and the SoA entries accurate between audits — without the work falling to calendar reminders and manual chasing.
In SureCloud, your asset register connects to identity, cloud, endpoint, and procurement feeds so it updates as the environment changes. Ownership is managed as a workflow: reassignment triggers fire when roles change, attestations are scheduled, and audit trails are immutable. Your SoA entries carry status, owner, linked evidence, and review cadence as live fields — not static text. Framework mappings for ISO 27001, DORA, and NIS2 move with the control, so one register produces regulator-specific views without duplication.
This is what GRC execution looks like. Not more data. More action from the same team.
30/60/90-Day Implementation Plan
First 30 days: Define scope and build foundations Confirm your A.8 scope and adopt the top-10 controls above as your first implementation wave. Connect IdP, cloud service providers, MDM/EDR, and ticketing to your asset register. Draft SoA applicability entries and document your exclusions with rationale.
Days 31–60: Close gaps and build evidence Close ownership gaps with named-role assignments and scheduled attestations. Roll out information classification where it is absent. Enable essential monitoring use-cases and set restore test cadences. Track the plan against target dates.
Days 61–90: Measure, map, and audit Track a small set of operational KPIs: MFA coverage, vulnerability remediation SLA adherence, log coverage, attestation completion rate. Map your ISO 27001 A.8 controls to DORA and NIS2 references. Run a targeted internal audit on A.8 and A.5.9–A.5.13 to confirm the register and SoA entries reflect operational reality.
Conclusion
Annex A.8 has two histories depending on which edition of ISO 27001 you are working from — and one consistent goal across both: keep your technology controls and asset management honest and provable.
A risk-based SoA that explains itself in one line per control is more defensible than a lengthy document full of promises. An asset register that updates continuously is more reliable than a spreadsheet that was accurate last November. ISO 27001 controls that map directly to DORA and NIS2 produce less duplicated work and better audit outcomes.
GRC isn't a data problem. It is an execution problem. When your controls, register, and evidence stay aligned between audits — not just at them — your ISMS works as a governance system, not a compliance exercise.
Your Business Assured.
References
-
ISO/IEC 27001:2022 — the standard
- IBM Cost of a Data Breach Report — breach cost data
- Verizon Data Breach Investigations Report — human element in breaches
- CISA Binding Operational Directive 23-01 — asset discovery frequency requirement
- DORA (EIOPA) — ICT asset management obligations
- NIS2 (ENISA) — risk management and asset identification requirements
Make Annex A.8 Work in Practice
FAQ’s
What is ISO 27001 Annex A.8 in the 2022 edition?
Annex A.8 in ISO/IEC 27001:2022 is the Technological controls theme — 34 controls covering the core technical safeguards for your ISMS: identity and privilege management, endpoint security, configuration management, backup and recovery, monitoring and logging, data leakage prevention, and secure development and change management.
What did Annex A.8 cover in the 2013 edition, and where are those controls now?
In ISO/IEC 27001:2013, A.8 was Asset management, covering inventory, acceptable use, ownership, return, classification, and labelling of information assets. In the 2022 edition, these controls were relocated to A.5 (Organisational controls), primarily A.5.9 through A.5.13. Media-handling controls were distributed across the Technological controls theme.
How do you decide which A.8 controls apply in your SoA?
Applicability is determined by your risk assessment, your technical architecture, your data types, and your supplier model. For each control, record whether it applies, the current implementation status, and a one-to-two line justification that names the driver. Reference the evidence that proves the status. A control without linked evidence is an unverified claim.
What evidence proves A.8 controls are effective?
Access reviews and PAM session logs for privilege controls. EDR deployment reports and vulnerability metrics for malware protection. Baseline documentation and drift reports for configuration management. SIEM use-case libraries with alert runbooks for monitoring. Backup job logs and restore test records for information backup. DLP incident trends and exception registers for data leakage prevention.
How does cloud shared responsibility affect your A.8 obligations?
It does not remove them. Cloud and SaaS providers manage their infrastructure; your obligations for identity, access, monitoring, configuration, and incident response remain yours. Document the boundary clearly in your SoA and supplier register. Then show the evidence for the controls on your side of that boundary.
“In SureCloud, we’re delighted to have a partner that shares in our values and vision.”
Read more on how Mollie achieved a data-driven approach to risk and compliance with SureCloud.
“In SureCloud, we’re delighted to have a partner that shares in our values and vision.”
Read more on how Mollie achieved a data-driven approach to risk and compliance with SureCloud.
“In SureCloud, we’re delighted to have a partner that shares in our values and vision.”
Read more on how Mollie achieved a data-driven approach to risk and compliance with SureCloud.
Platform +
Frameworks +
Products +
Industries +
Resources +
Company +
London Office
1 Sherwood Street, London, W1F 7BL, United Kingdom
US Headquarters
6010 W. Spring Creek Pkwy., Plano, TX 75024, United States of America
© SureCloud 2026. All rights reserved.
.webp)



