.png?width=189&height=505&name=Vector%20(2).png)
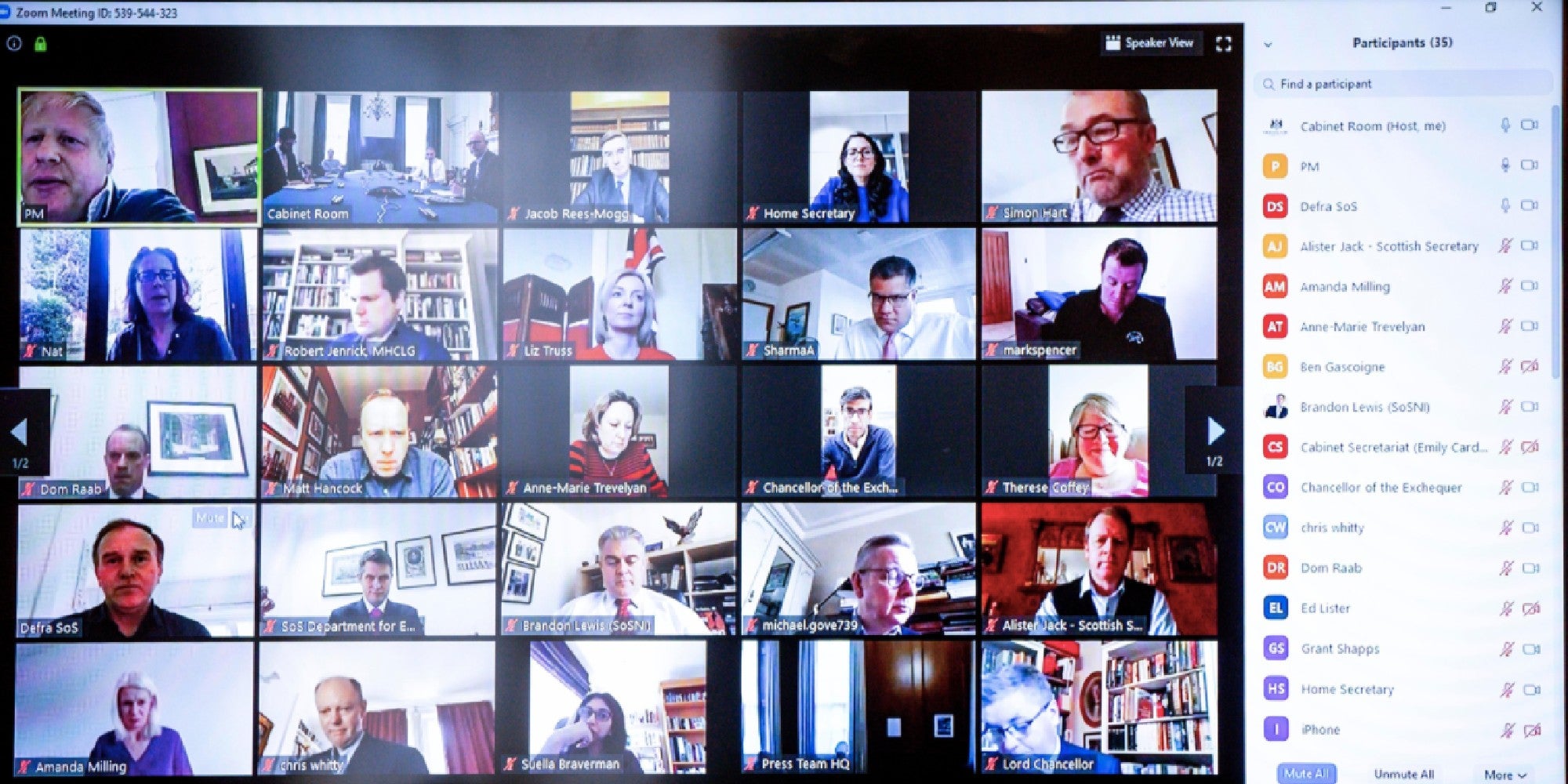
How to stay secure when using video conferencing and communication channels
ollowing on from the FBI warning about cybersecurity while using the American remote conferencing services company Zoom, due to the rise in “Zoombombing” our Principal Cybersecurity Consultant Elliott Thompson gives us his view on what the real risk of using Zoom is and the tips for how you can mitigate the security threats.
What is the key security/privacy issue of Zoom and other video conferencing tools?
The main ongoing privacy concern with Zoom is that the employees of Zoom can view people’s video/audio. This doesn’t mean they do, but architecturally they can. The same is also true for Teams, Skype and most other video conferencing systems.
Disclosed vulnerabilities in Zoom
Separate from the overall way that Zoom works, there have been several publicly disclosed vulnerabilities:
- 2018 – Manipulate meetings/send fake messages
- 2019 – Force users to join malicious video calls
- 2019 – Critical code execution
- 2019 – Webcam information disclosure
- 2020 – MacOS Local Privilege Escalation
There have been some serious flaws affecting almost all Zoom products. And in some cases, the fixes that have been put in place have been undone by later patches. While Zoom does seem to have more than their fair share of vulnerabilities, it is not the only video conferencing tool with these kinds of flaws; for example, Cisco WebEx had an extremely critical code execution vulnerability that was found in 2017.
What are your business objectives?
There is definitely an increased risk of using any application like Zoom/WebEx. But whether that risk is acceptable is up to the organisation. For some businesses, the features outweigh the risk, for others, the risk is too high no matter what the features are. Like anything – you have to take a risk-based approach to the tools and technologies used.
Zoom’s proactive stance
One point to also consider is that Zoom is getting a significant amount of attention and so far seem to be proactively responding and actively improving their security posture. There are many, many more flaws in many, many other products that are simply not even known about yet or haven’t had the attention for them to be found.
Key steps you can take to help mitigate security risks in Zoom:
1) Ensure that any local Zoom clients and browser plugins are kept fully up to date.
2) Ensure that all Zoom meetings have strong passwords set which are not ‘shared’ between separate meetings.
3) Disable the ‘telephone dial-in’ option wherever possible. The reason for this is because you only need a meeting ID to connect via telephone dial-in, not the meeting ID and a password like you do for computer-based audio.
4) Monitor participants of the meeting and ensure that only those expected at present.
5) Ensure that the username and password you have set for you Zoom account are unique and not shared with any other system or service.
6) Enable two-factor authentication on your Zoom account.
Conclusion
To summarise, if the meeting/conversation is highly sensitive – consider the risks, aligned to your organisation’s risk methodology/process.
These tips are here to help you rather than scare. If you have questions or concerns, please email services@surecloud.com, and we will do our best to assist you.
Or check out my other blog, which is a Q&A discussing COVID-19 risks during this WFH era, and includes the exposure consumer-grade video conferencing could bring as outlined above.
.png?width=265&height=582&name=Vector%20(3).png)









.png?width=286&height=582&name=Vector%20(7).png)

 Copy link
Copy link

