Take Control of Cyber Risk
SureCloud brings together your risks, vulnerabilities, and control data into a single cyber risk management software—so you can reduce cyber risk across your entire business. See the full picture, act faster, and deliver audit-ready, role-based reporting—so you always know where risk is rising and how to respond.
Trusted by organizations where cyber risk is business risk
Identify threats faster, strengthen defenses, and protect what matters most.
SureCloud is trusted by global enterprises in finance, healthcare, and government. Our platform helps teams stay compliant, respond to threats faster, and maintain confidence with clear, unified cyber risk management.
Downloads
Download to discover more insights and features on how to manage your Risk and Compliance with SureCloud:
Fragmented data, manual processes, and slow response put your business at risk
Managing cyber risk with scattered spreadsheets, disconnected tools, and inconsistent processes leaves teams struggling to see threats—or act on them—before they become incidents.
Unified Threat & Vulnerability Register
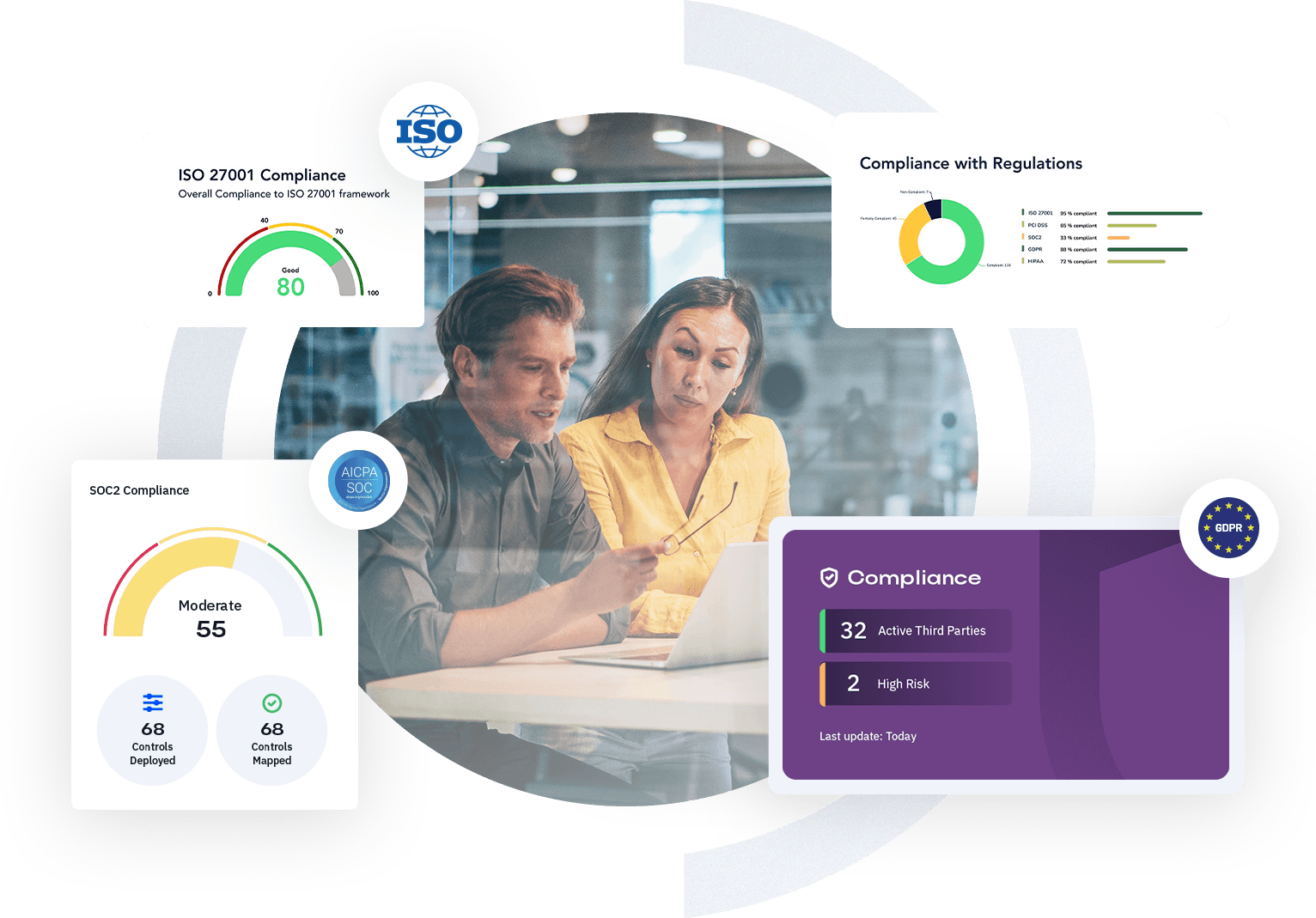
Role-Based Dashboards for Every Team
Give leadership, security, and IT real-time visibility into risk status, remediation progress, and control maturity with dashboards tailored for each audience.
Automated Remediation Workflows
Trigger escalations, assign tasks, and follow up automatically so nothing falls through the cracks—speeding up your response and reducing manual effort.
Audit-Ready Reporting & Evidence
Export compliance reports, audit trails, and evidence packs mapped to frameworks like ISO 27001, DORA, and NIS2 in a few clicks.
Cyber risk management software built for clarity, speed, and action
One cyber risk management platform for your whole organization

Real-time dashboards that drive action
Executive dashboards and drill-down views help leadership and teams focus on what matters most—so risk, remediation, and compliance are always in sync.
Automated workflows and ownership
Assign owners, set escalation paths, and automate follow-up so every task is tracked, documented, and closed out—reducing response times and missed steps.
Evidence-ready, always
Generate audit-ready reports and compliance evidence on demand. Stay prepared for audits, regulatory reviews, and board updates with accurate, current data.
Built to fit your environment
Out-of-the-box integrations connect SureCloud to your existing SIEM, ITSM, and vulnerability tools—streamlining data flows and reducing manual effort.
Flexible, scalable, and secure
Start fast with core risk and reporting tools, and scale up to advanced integrations, multi-framework compliance, and granular access controls as your needs evolve.
Scales as Your Business Grows
Stop wasting time on manual compliance tasks. Automate workflows, streamline compliance with Continuous Control Monitoring (CCM), and collect evidence effortlessly to ensure you’re always audit-ready with minimal effort.
FAQs
Can I migrate our existing risk register?
Yes. Import your current risk data directly into SureCloud’s cyber risk register to keep everything in one place.
What’s the difference between Foundations and Enterprise?
Foundations provides fast, simple cyber risk management for growing teams. Enterprise adds more cyber risk automation, integration, and scale for complex environments.
Does this integrate with our security stack (SIEM, ticketing)?
Absolutely. SureCloud’s cybersecurity compliance software connects with key security tools and systems, so you always have the latest context.
Can I report risk posture to execs and auditors?
Yes. Use SureCloud’s dashboards and reports to keep leaders and auditors up to date on your cyber risk posture.
Do you support multi-framework compliance (NIST, ISO, etc.)?
Yes. SureCloud aligns with ISO 27001, NIST Cybersecurity Framework, DORA, and more for complete cybersecurity compliance.
The Risk and Compliance Management platform that scales with your business

Prices from:
£15,000 per year
Get compliant and stay compliant faster.
Foundation reduces the effort to meet and maintains compliance (SOC2 or ISO27001) standards by 60%.

Unlock the value within your risk and compliance landscape.
Respond to changes in your risk and compliance landscape 50% more efficiently with centralised Dynamic Risk Intelligence real-time monitoring and reporting.

The Risk Reckoning is here.
Are you ready?
Based on research with 200+ UK GRC leaders, this exclusive report from SureCloud reveals the real-world disconnects, pressures, and priorities shaping Governance, Risk, and Compliance today.
%
Only 45% have an integrated approach to risk and compliance
%
87% of executives claim they're prepared for a major GRC
%
98% say GRC maturity is key to operational
Get the insights 200+ GRC leaders are acting on
"Their transparent approach made the process feel collaborative and constructive, creating a solid foundation for a productive partnership.”

Read more on how Specsavers achieved a proactive approach to risk and compliance with SureCloud.
“SureCloud’s solution has brought a comprehensive clarity to data processing that was impossible to achieve with spreadsheets.”

Read more on how Everton FC achieved GDPR with SureCloud
“In SureCloud, we’re delighted to have a partner that shares in our values and vision.”
Read more on how Mollie achieved a data-driven approach to risk and compliance with SureCloud.




